Hacker-chasing Check Point analysts hone their skills in the wizarding world
Pioneering Israeli cybersecurity firm’s research team just found a Russia-based ransomware scam, a recent development in the threat landscape it is constantly monitoring
Cybersecurity researchers at Israel’s Check Point Software Technologies have lately stumbled upon a new and worrying development in the ransomware industry.
Ransomware is a computer hack in which criminals penetrate computers, take their data hostage, and demand a ransom for its release. Some companies often pay out money to get their data back, but others hire an IT consultancy to help them unlock their files. According to Europol’s 2018 Internet Organized Crime Threat Assessment, the ransomware industry now drains some $5 billion a year from our economy.
The threat intelligence researchers at Check Point came across a Russian IT consultancy, promoted online as Dr. Shifro, who claimed to be able to help victims of a ransomware attack to unlock their encrypted files. But the firm was actually working with the hackers, sharing its profits with them, the researchers said in a blog post published on Monday exposing the scam.
The researchers’ suspicions were raised when they noticed Dr. Shifro was offering just one service: helping ransomware victims unlock their files. For an IT consultancy to offer only one unique service was highly unusual, they felt. Not only that, Dr. Shifro was promising potential clients that it could unlock files held ransom by the Dharma/Crisis attack, for which the Israeli researchers knew no decryption key was available. And whereas IT services normally say they will do their best to help their clients, Dr. Shifro offered a guarantee.

So the researchers did some undercover investigating and came to the conclusion that Dr. Shifro was contacting with the creators of the ransomware and making a deal with them to unlock the victim’s files in return for a discounted ransom payment, a price Dr. Shifro would then pass on to the customers along with its own fee charges.
“The business model that Dr. Shifro has created is an attractive one that could easily be replicated by other entrepreneurial scam artists and thus serves as a new development of the ransomware industry that both individuals and organizations should be wary of,” wrote the Check Point researchers in the blog.
A $17 billion anti-hacking powerhouse
Check Point Software, founded in 1993 by Gil Shwed, Marius Nacht and Shlomo Kremer, is valued at $17 billion, making it Israel’s second largest publicly traded company and the oldest and one of the largest cybersecurity firms globally, with some 100,000 customers worldwide and 5,000 employees, 2,200 of them in Israel.
Its team of cyber-intelligence researchers — some 200 based in Tel Aviv — is one of the largest in the industry. It is made up of a wide variety of motivated young men and women, many of whom come from intelligence units of the Israeli army, who are eager to find out what new threats lurk in the dark underworld of hackers, cybercrime, and virtual terror attacks.

“Our role is to protect our customers and also find new threats,” said 32-year old Maya Horowitz, the director of Check Point’s Threat Intelligence and Research unit in Tel Aviv, who joined the firm in 2014 after serving for 10 years in the IDF’s legendary 8200 elite technology unit, working on cybersecurity projects.
“When I joined the army, the word cyber didn’t even exist yet,” she said. “It was the very beginning of the phenomenon.”
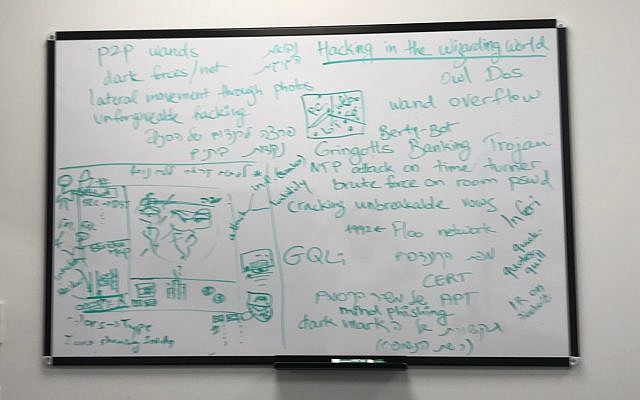
Post-It notes cluttered her desk and she quickly shoved away a brown paper lunch bag as she posed for a picture for The Times of Israel. On a whiteboard on one of the walls there are handwritten scribbles and charts: Owl Dos, wand overflow, P2P wands, dark forces/net, unforgivable hacking, the writings said.
Is that information on another attack? this reporter asked. “No,” Horowitz answered with a shrug. “It’s about Harry Potter,” referring to the main character in the fantasy novels written by British author J.K. Rowling. “We are just imagining how cybersecurity would look in the wizarding world.”
That’s what these researchers do for fun, in the little time they have between going through customer logs reporting attacks and surfing the dark web looking for signals of an impending attack.
The work of the researchers — many of whom are data, intelligence and malware analysts and reverse engineers — is to identify threats and threat actors, find out what they are doing and what they are planning. Intelligence analysts in the team dig down into malicious files, but also scour web and dark web forums, social media, and cloud-based messaging services, to try to find the bigger picture behind an attack. When they find the culprits or a vulnerability, they report their findings to the relevant authorities or to the companies affected by the hack.
“Our software knows to identify an attack and halt it, but also to tell customers what kind of an attack it is,” said 31-year old Lotem Finkelstein, who heads the threat intelligence desk at Check Point, which he joined in 2015 after serving in an IDF intelligence unit.
When the software at a client foils an attack, the Check Point researchers automatically – and with the agreement of their clients – get a report, or log, on the attack.

For privacy reasons, the researchers don’t know the source of the log, but they combine them with other logs to get a full picture of the threat landscape and attacks that are happening at any given time from the 100,000 clients they have around the world, many of them Fortune 500 firms.
The researchers collect that data and provide the information to Check Point’s product development unit, so that new products can be updated to include the new threats and to warn clients and immediately update existing software platforms with new protections.
This software update “happens millions of times a day,” said Horowitz, through a process of automation and human input.
That is the advantage of being a big firm, Horowitz and Finkelstein said: You get a bigger picture.
The Check Point researchers have helped expose many attacks and hackers.
They informed Huawei Technologies Co. about a vulnerability in its routers; warned that old office fax machines can be a backdoor for hackers; and sounded the alarm about a security flaw in the instant messenger WhatsApp, in which hackers could intercept and manipulate messages, and about a weakness in Chinese drone systems that could have led to hacks.
They were also “involved” they said, without elaborating further, in revealing a scam set up by the Palestinian Islamist group Hamas that tried to install spyware on Israeli soldiers’s cellphones through a malicious app that purported to help its targets keep track of World Cup scores and through two fake online dating sites.
Check Point and its researchers don’t get paid for exposing these hacks.
“We see it as an obligation to the community,” Horowitz and Finkelstein said, adding that they work closely with the FBI, Europol, Interpol and the Israeli crime fighting unit Lahav 433.
To do their work, said Horowitz, the researchers must have a “passion” for digging into the details of software code. Each and every one of them had the skills to work in the dark side of industry, but they “enjoy being part of the good side,” she said. “It is all about ideology.”
The company, which reported revenues of $1.86 billion in 2017, does benefit from the prestige it gets from revealing the hacks, they acknowledged. Delegations from around the world make pilgrimages every day to the firm’s headquarters in Tel Aviv to gain insight into cybersecurity and hacking news.
Threats today are different from what they were once, said Horowitz. “There are many more platforms now” on which a hack can occur, she said, with attacks moving from servers and computers to smartphones, internet of things (IoT) devices, smart cars and the cloud. “Hackers can catch us in different places with exactly the same attack,” she said. “So the risk is so much bigger.”

While cybersecurity attacks were once “mass attacks” targeting large numbers of people indiscriminately, attacks are now more “boutique,” where threat actors “invest a lot of time penetrating specific organizations and spreading malware or ransomware” at critical junctions of corporations.
China and Russia are the two main players in nation-sponsored attacks, said Finkelstein. North Korea is also “very active,” setting up brutal attacks like that of the Lazarus hacking group, believed to be behind a massive $81 million cyber-heist from the Bangladesh Central Bank (BCB) in 2016, and also behind the WannaCry ransomware attack, among others.
“Iran is not in the same league,” as China and Russia, he added, though in the Middle East the Hamas is “very active” targeting both Israel and the Palestinian Authority.
Still, she said, anyone can become a hacker by just buying tools and malware on the dark web or in forums. “Everyone who has bad intentions can now start an attack,” she said.

She died more than four decades ago, but Leah Goldberg remains a magnetic and enigmatic figure: Israel’s most beloved poet, a powerful woman who lived with her mother and never married, who reinvented herself from the ashes of World War I through her magical writing.
You can screen 'The Five Houses of Leah Goldberg' June 4-11. Join The Times of Israel Community today to support our work and watch this and other outstanding documentary films in our DocuNation series.

We’re really pleased that you’ve read X Times of Israel articles in the past month.
That’s why we started the Times of Israel - to provide discerning readers like you with must-read coverage of Israel and the Jewish world.
So now we have a request. Unlike other news outlets, we haven’t put up a paywall. But as the journalism we do is costly, we invite readers for whom The Times of Israel has become important to help support our work by joining The Times of Israel Community.
For as little as $6 a month you can help support our quality journalism while enjoying The Times of Israel AD-FREE, as well as accessing exclusive content available only to Times of Israel Community members.
Thank you,
David Horovitz, Founding Editor of The Times of Israel
The Times of Israel Community.