Israel is one of at least 74 countries hit by massive extortion cyberattack
Security firms record more than 45,000 attacks worldwide as fast-spreading ‘ransomware’ hits hospitals, health systems, telecoms
Israel is among over 70 countries hit by a massive, fast-moving cyberattack that exploited a flaw exposed in documents leaked from the US National Security Agency, security firms indicated Friday.
Two security firms — Kaspersky Lab and Avast — said they had identified the malware behind the attacks, indicating that Russia was the hardest hit.
A world map showed Israel among those affected but on a low scale alongside regional neighbors Jordan, Egypt, Iran and Saudi Arabia. Low-level attacks were also recorded in Canada, the US, most of South America and Europe.
It was not immediately clear which industries or companies in Israel were affected.
#WannaCry #ransomware used in widespread attacks all over the world via @Securelist https://t.co/zh012F9lCC pic.twitter.com/UzJVqUwbT6
— Kaspersky (@kaspersky) May 12, 2017
India, Ukraine and Kazakhstan were more severely hit, as shown on the map.
The Russian Interior Ministry has confirmed it was hit by the “ransomware” attack, which encrypts data on infected computers and demands payment, usually via the digital currency bitcoin, to release it. Britain’s health service was also hit hard Friday as the attack froze computers at hospitals across the country, shutting down wards, closing emergency rooms and bringing medical treatments to a screeching halt.
The attacks — which experts said affected dozens of countries — used a technique known as ransomware that locks users’ files unless they pay the attackers a designated sum in the virtual currency bitcoin.
Affected by the onslaught were computer networks at hospitals in Britain, the Spanish telecom giant Telefonica and the US delivery firm FedEx and many other organizations.
Britain’s National Cyber Security Centre and its National Crime Agency were looking into the UK incidents, which disrupted care at National Health Service facilities.
“This is not targeted at the NHS, it’s an international attack and a number of countries and organizations have been affected,” British Prime Minister Theresa May said.
Russia’s interior ministry said that some of its computers had been hit by a “virus attack” and that efforts were underway to destroy it.
36,000 detections of #WannaCry (aka #WanaCypt0r aka #WCry) #ransomware so far. Russia, Ukraine, and Taiwan leading. This is huge. pic.twitter.com/EaZcaxPta4
— Jakub Kroustek (@JakubKroustek) May 12, 2017
The US Department of Homeland Security’s computer emergency response team said it was aware of ransomware infections “in several countries around the world.”
Jakub Kroustek of the security firm Avast said in a blog post update around 2000 GMT, “We are now seeing more than 75,000 detections… in 99 countries.”
Kaspersky researcher Costin Raiu cited 45,000 attacks in 74 countries, saying that the malware, a self-replicating “worm,” was spreading quickly.
In a statement, Kaspersky Labs said it was “trying to determine whether it is possible to decrypt data locked in the attack — with the aim of developing a decryption tool as soon as possible.”
‘Unequivocally scary’
“It’s unequivocally scary,” said John Dickson of the Denim Group, a US security consultancy.
Dickson said the malware itself, which exploits a flaw in Windows, was not new but that adding the ransomware “payload” made it especially dangerous.
“I’m watching how far this propagates and when governments get involved,” he said.
The malware’s name is WCry, but analysts were also using variants such as WannaCry.
https://twitter.com/MalwareTechBlog/status/863054943632187392
Forcepoint Security Labs said in a statement that the attack had “global scope” and was affecting networks in Australia, Belgium, France, Germany, Italy and Mexico.
In the United States, FedEx acknowledged it had been hit by malware and was “implementing remediation steps as quickly as possible.”
Britain’s National Health Service declared a “major incident” after the attack, which forced some hospitals to divert ambulances and scrap operations.
Message to users: ‘Oops’
Pictures posted on social media showed screens of NHS computers with images demanding payment of $300 (275 euros) in bitcoin, saying: “Ooops, your files have been encrypted!”
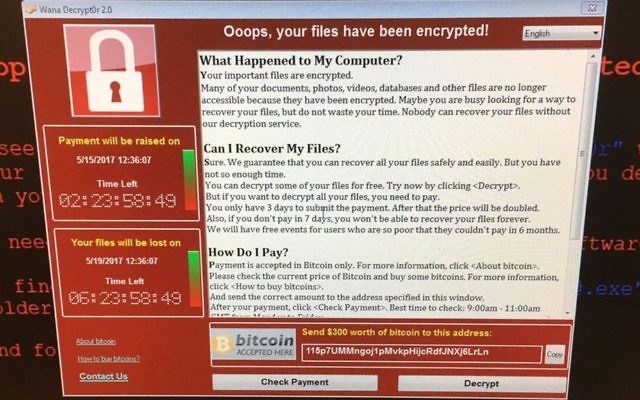
It demands payment in three days or the price is doubled, and if none is received in seven days, the files will be deleted, according to the screen message.
A hacking group called Shadow Brokers released the malware in April claiming to have discovered the flaw from the NSA, Kaspersky said.
Although Microsoft released a security patch for the flaw earlier this year, many systems have yet to be updated, researchers said.
“Unlike most other attacks, this malware is spreading primarily by direct infection from machine to machine on local networks, rather than purely by email,” Lance Cottrell, chief scientist at the US technology group Ntrepid.
“The ransomware can spread without anyone opening an email or clicking on a link.”
The sort of ransom demands have been growing precedent at medical facilities. In February 2016, a Los Angeles hospital, the Hollywood Presbyterian Medical Center, paid $17,000 in bitcoin to hackers who took control of its computers for more than a week.
“Ransomware becomes particularly nasty when it infects institutions like hospitals, where it can put people’s lives in danger,” said Kroustek, the Avast analyst.
A spokesman for Barts Health NHS Trust in London said it was experiencing “major IT disruption” and delays at all four of its hospitals.
“We have activated our major incident plan to make sure we can maintain the safety and welfare of patients,” the spokesman said. “Ambulances are being diverted to neighboring hospitals.”
Two employees at St Bartholomew’s Hospital, which is part of Barts Health, told AFP that all the computers in the hospital had been turned off.
Caroline Brennan, 41, went to the hospital to see her brother, who had open heart surgery.
“They told us there was a problem. They said the system was down and that they cannot transfer anyone till the computer system was back up,” Brennan said.
Some said the attacks highlighted the need for agencies like the NSA to disclose security flaws so they can be patched.
“These attacks underscore the fact that vulnerabilities will be exploited not just by our security agencies, but by hackers and criminals around the world,” said Patrick Toomey of the American Civil Liberties Union.
The Times of Israel Community.












