Israeli hacker game could beat Russian web crooks
No one knows how a Russian gang stole 1.2 billion passwords, but gaming Checkmarx wants to stop a recurrence
An Israeli company has put out a game that is not just for fun — it’s meant to prevent recurrence of the giant hack that a netted Russian gang 1.2 billion usernames and passwords in the “Heartbleed” fiasco. If it wasn’t obvious before, this backs up the insistence of Checkmarx that it’s time for attention to Internet security to move to the front seat.
If the UN’s statistics are correct, that 40% of the world’s 7.1 billion people use the Internet, then Russian hackers own one out of every three personal logins for social media sites, email, banking sites, and who knows what else, according to reports. How the Russian hackers got access to more than 1 billion usernames and passwords from hundreds of thousands of websites is a mystery — the company that unveiled the information, Hold Security, isn’t saying — but it could very well be connected to the enormous multi-year security foul-up that affected the Internet’s main security protocol, OpenSSL.
That security hole, which was apparently around for years before anyone noticed, is believed to have affected nearly one out of every five secure web servers — the ones that are supposed to be safe for submitting credit card information. According to some experts, Heartbleed is perhaps the biggest and worst security breach ever to hit the Internet. Why nobody noticed isn’t clear, according to Maty Siman, CTO and founder of Israeli security company Checkmarx, but it could be connected to the “back seat” security has often taken for programmers.
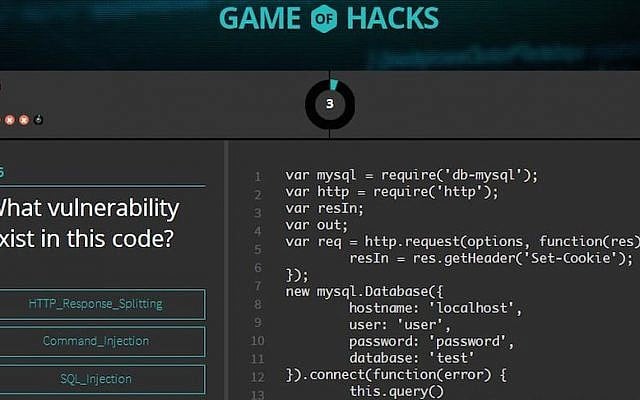
It’s a problem Checkmarx has been concerned with for some time now — and to improve programmers’ grasp of security issues, Checkmarx this week released the “Game of Hacks,” an online contest programmers can play against or computer — or each other — to help them identify the dumb mistakes programmers often make that opens the door to web thieves, who are able to easily penetrate site defenses and grab whatever data they want.
Heartbleed was the name given to a bug that was discovered in early April in the Internet’s Transport Layer Security (TLS) protocol, the open-source OpenSSL cryptography library. The bug, according to experts, may have been around for years.
Heartbleed was avoidable in many cases. An observant programmer, said Siman, would have avoided writing the code that enabled hackers to use the Heartbleed protocol to invade servers. “Heartbleed is a bug in the basic implementation of open-source OpenSSL. Many security problems, like Heartbleed, can be traced to the original code written by programmers — in which they added features without checking the security ramifications,” said Siman.
That’s where Game of Hacks comes in. The game, available for desktop, tablet and mobile, presents the developer with vulnerable pieces of code and challenges them to identify the application layer vulnerability as quickly as possible. It’s designed for both beginning and advanced programmers, covering hacker “top 10 favorite” vulnerabilities like SQL injection, XSS, Log Forgery, Path traversal, Parameter Tampering, and many other esoteric terms that make the eyes of ordinary people glaze over, but cause dollar signs to flash in hackers’ eyes.
Checkmarx announced the game this week at the annual Blackhat cyber-security convention in Las Vegas, which is incidentally where the Russian hack breach was announced — and that turned into the talk of the town. According to Held, the hackers are using the purloined usernames and passwords mostly to send spam to social network and e-mail accounts — but no one at this time really knows the extent of the damage, and how many passwords the hackers have stolen for banking, insurance, government, and infrastructure sites.
Shockingly, said Asaph Schulman, VP of marketing of Checkmarx, the tactics used by hackers are similar, no matter what the exploit — and those tactics can be stopped. “We’ve been seeing a rise in hackers successfully exploiting vulnerabilities in applications’ codes — vulnerabilities that often exist from the early development stage of the software and remain undetected until it’s too late. We repeatedly hear security managers concerned about the secure coding knowledge of their development teams and looking to provide more training. Game of Hacks was designed to sharpen developers’ security acumen in a fun and interactive way so many of the most common security vulnerabilities can be avoided in the first place.”
The first step to stopping a hacker is thinking like one, said Siman — and that means enabling programmers to see what a hacker sees from a vulnerability point of view. That is what Game of Hacks is all about. “Checkmarx is committed to bridging the gap between app developers’ coding abilities and their security literacy,” said Siman. “Thinking like a hacker can ensure developers protect their applications from the most likely exploits. As mobile and web applications grow in popularity, protecting consumer information before it is put at risk is more important than ever.”
The Times of Israel Community.