Cyber ‘cold war’ rages online but Russia holds back on massive digital attacks
Destructive global breaches have not yet materialized, observers say, as non-state actors and hacktivists engage in digital combat
While the Russian military inflicts devastating destruction in Ukraine three weeks into the invasion of its neighbor, Russia and Western countries are engaged in a cyber “cold war” that has yet to escalate, according to a top Israeli cyber specialist.
Russia has powerful offensive cyber capabilities that have previously wreaked malware havoc on global systems, “but we haven’t yet seen any meaningful cyber weapons in this conflict,” said Moshe Karako, a 20-year veteran of the cybersecurity space who serves as chief technology officer at NTT Innovation Laboratory Israel.
Karako told The Times of Israel in a phone interview that there have been three main types of cyberattacks so far from both sides, but mainly Russia.
First, Moscow deployed “wiper” attacks — a type of malware attack that seeks to destroy data, wiping it from systems — against Ukrainian targets before the invasion and on the first day of the military assault on February 24, which also infected computers in neighboring Latvia and Lithuania.
“This is done to create chaos. There’s no request for ransom. It’s a psychological weapon that also causes problems in supply chains and affects finances,” Karako described, adding that these types of weapons have been used quite a bit.
A 2017 cyberattack on Ukraine attributed to the Russian government and state actors Russia has been called the “worst cyberattack” with global dimensions. NotPetya spread across the world from hospitals to shops to banking multinationals, huge corporations, and manufacturers, and cost billions of dollars in losses. The “wiper” caused more than $10 billion of damage globally by infecting companies that do business in Ukraine with malware seeded through a tax preparation software update.
Three weeks into Russia’s war on Ukraine, researchers are still mapping out the wiper malware on Ukrainian systems.

The second type of attack, said Karako, was from the Ukrainian side. Ukraine has recruited a global volunteer “hacktivists” corps engaged in digital combat that includes denial-of-service attacks on official Russian sites, intelligence-gathering, disinformation-countering, and general messaging.
“They bombard the other side with requests for access to cause DDoS [distributed denial-of-service]. This affects banks, transactions, government services to citizens, and so on,” he said, later adding that these attacks have not yet caused very serious damage.
The third cyber front is in the information realm, “where false information is deliberately created” to spread confusion and disinformation.
“They hack sites to alter messages, information, and to create chaos,” he said.
A recent example is a cyberattack Wednesday on a Ukrainian news channel where a chyron appeared falsely saying Ukraine surrendered to Russia. A circulated deepfake video this week of Ukrainian President Volodymyr Zelensky appearing to tell Ukrainians to surrender has also added to the chaos and confusion.
Cyber fronts
In addition, “like in an actual war, people here are taking an active part, and companies too,” said Karako in reference to a corporate boycott of over 400 global companies including tech firms, major manufacturers, and consumer brands that have either suspended or halted their operations in Russia altogether or have restricted their services to pressure the Kremlin over the war, according to a running tally kept by a team of researchers from Yale University. The list includes Visa, Apple, Facebook, Mastercard, Amazon, Google, Ford, Dell, DHL, and McDonald’s.
This global campaign to punish Russia is in addition to the crippling sanctions Western governments have imposed on Russian industries, leadership, and key figures to push Russian President Vladimir Putin to stop the war. Sanctions have been imposed by the US, the UK, the EU, Canada, Japan, Singapore, South Korea, Taiwan, Australia, and New Zealand.
And responses to some of these sanctions are taking place behind the scenes. Karako pointed to a February 28 incident — four days after Russia’s invasion — when Japan announced that it was joining in with US sanctions against Russia by blocking banks from accessing the SWIFT international payment system, after which Toyota, a major Japanese carmaker, was forced to temporarily suspend domestic factory operations following a major cyber attack on a critical supplier.
“You have the punishment of a civilian organization [with the aim of] applying pressure on the leadership. This is concerning for everyone. A cyberwar pulls in people and organizations very easily,” said Karako.

Some cyber vulnerabilities or exploits “are known for days, weeks, months ahead of time, and they put it into action when it’s needed,” he said. “Hackers build banks of targets to use.”
Karako called this environment “a cyber ‘cold war'” in which nations have been gathering capabilities that “allow them to put pressure on other countries and create an impact without jeopardizing forces or crossing any physical borders.”
These capabilities include targeting critical infrastructure to hit “power companies, nuclear systems, water systems — anything that supports physical life. This already exists,” said the cyber specialist.
He believes Russia has not used some of these “doomsday” weapons for two reasons: “One, Russia believed it has already won the war, with tanks on the ground, with the destruction, and two, a doomsday weapon can only be used once — because the community of cyber defenders will find solutions and this attack is very costly and triggers reactions.”

Offensive tools and deterrence
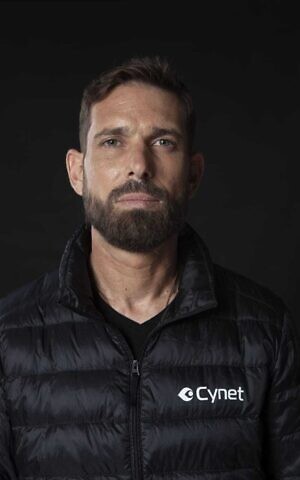
Shiran Grinberg, director of research and cyber operations at Israeli cybersecurity company Cynet, told The Times of Israel that “the Russians have learned from their own mistakes with attacks like NotPetya and others like WannaCry [a destructive malware attack in 2017 attributed to North Korea].”
“In many cases, Russia suffered as well because these attacks are very destructive. Ukraine was the target [in NotPetya], but it also ended up affecting Russian networks as well,” said Grinberg.
“Russia is actively invading Ukraine and it needs some of its infrastructures to help its forces,” he explained.
The danger in this current crisis, he said, was the “huge amount of offensive tools that malicious actors can leverage” since non-state hackers and hacktivist groups are also taking part in the war.
Grinberg referenced the 2020 discovery that powerful CIA hacking tools were breached and leaked online where they could be accessed.
He said that as a security provider, Cynet works with enterprises and organizations to identify security loopholes and conduct threat intelligence to cover as many attack vectors on an endpoint level (end-user devices like laptops, desktop computers, and mobile devices) as possible.
Cynet’s research group, which he heads, is charged with “developing detection mechanisms and catching bad guys,” Grinberg said. The Israeli company had two development teams in Ukraine before the war, he said, adding that some managed to leave while others stayed to fight.
Nate Fick, VP of security strategy at Elastic NV, an open code software giant co-founded by Israeli entrepreneur Shay Banon, said that “a decade ago, we couldn’t imagine the extent to which private organizations would be made responsible for defending themselves against a nation-state attack.
“But as we’ve seen with recent cyberattacks, that is exactly what is being asked of them,” Fick said in a written exchange with The Times of Israel this week.
Fick said one reason we may have yet to see a massive cyberattack by Russia was deterrence. The US and others have warned Moscow against using such attacks and have threatened to fire back.

US President Joe Biden said in a briefing on the first day of Russia’s invasion of Ukraine: “If Russia pursues cyberattacks against our companies, our critical infrastructure, we are prepared to respond.”
“Hopefully, this means that deterrence — at least so far — is working,” said Fick. “Deterrence in the cyber domain can take a couple of different forms. First is the kind of deterrence ‘by response,’ such as that provided by President Biden’s statement. But deterrence ‘by denial’ is also important, such as persuading the Russians that Western defenses are good enough that they would be unlikely to have widespread success with attacks on critical infrastructure.”
Although Russia has certainly been “using cyber attacks and disinformation/misinformation attacks against Ukraine as part of its military action there,” there is no evidence of Russian cyberattacks against the US, NATO, or other targets as “all sides thus far seem to agree that attacks on critical infrastructure outside Ukraine would be significantly escalatory,” said Fick.
The US Congress last week approved new rules that require companies critical to US national interests to report when they’ve been hacked or have paid ransom following a ransomware attack.
The rules are part of a broader effort by the Biden administration and Congress to shore up US cyber defenses. The reporting will give the federal government much greater visibility into hacking efforts that target private companies, which often have skipped going to the FBI or other agencies for help.
It requires any entity that’s considered part of the nation’s critical infrastructure, which includes the finance, transportation, and energy sectors, to report any “substantial cyber incident” to the government within three days and any ransomware payment made within 24 hours.
Fick said governments should work more collaboratively to fend off attacks. “Reporting foundational intelligence for key adversaries while collaborating with private-sector intelligence and internet security companies could significantly enhance the ability to attribute future attacks to our systems swiftly. This would create real-time shared situational awareness across multiple jurisdictions, ultimately better defending a nation’s interests.”
AP contributed to this report.

She died more than four decades ago, but Leah Goldberg remains a magnetic and enigmatic figure: Israel’s most beloved poet, a powerful woman who lived with her mother and never married, who reinvented herself from the ashes of World War I through her magical writing.
You can screen 'The Five Houses of Leah Goldberg' June 4-11. Join The Times of Israel Community today to support our work and watch this and other outstanding documentary films in our DocuNation series.

We’re really pleased that you’ve read X Times of Israel articles in the past month.
That’s why we started the Times of Israel - to provide discerning readers like you with must-read coverage of Israel and the Jewish world.
So now we have a request. Unlike other news outlets, we haven’t put up a paywall. But as the journalism we do is costly, we invite readers for whom The Times of Israel has become important to help support our work by joining The Times of Israel Community.
For as little as $6 a month you can help support our quality journalism while enjoying The Times of Israel AD-FREE, as well as accessing exclusive content available only to Times of Israel Community members.
Thank you,
David Horovitz, Founding Editor of The Times of Israel
The Times of Israel Community.










